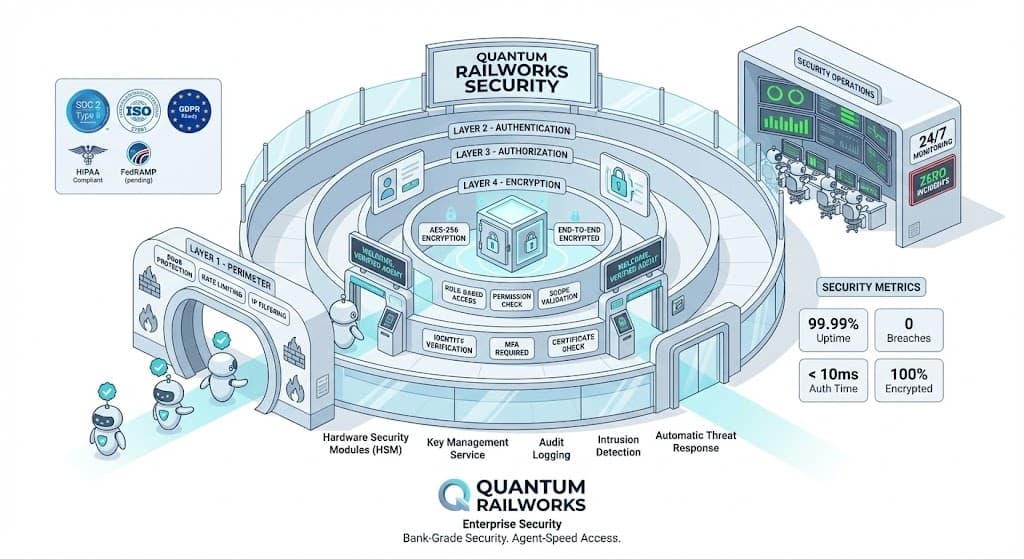
Bank-Grade Security for Autonomous Commerce
Every layer of Quantum Railworks is designed with security-first principles. From cryptographic identity to immutable audit trails, your transactions are protected.
Defense in Depth
Multiple security layers ensure that even if one defense is compromised, your data and transactions remain protected.
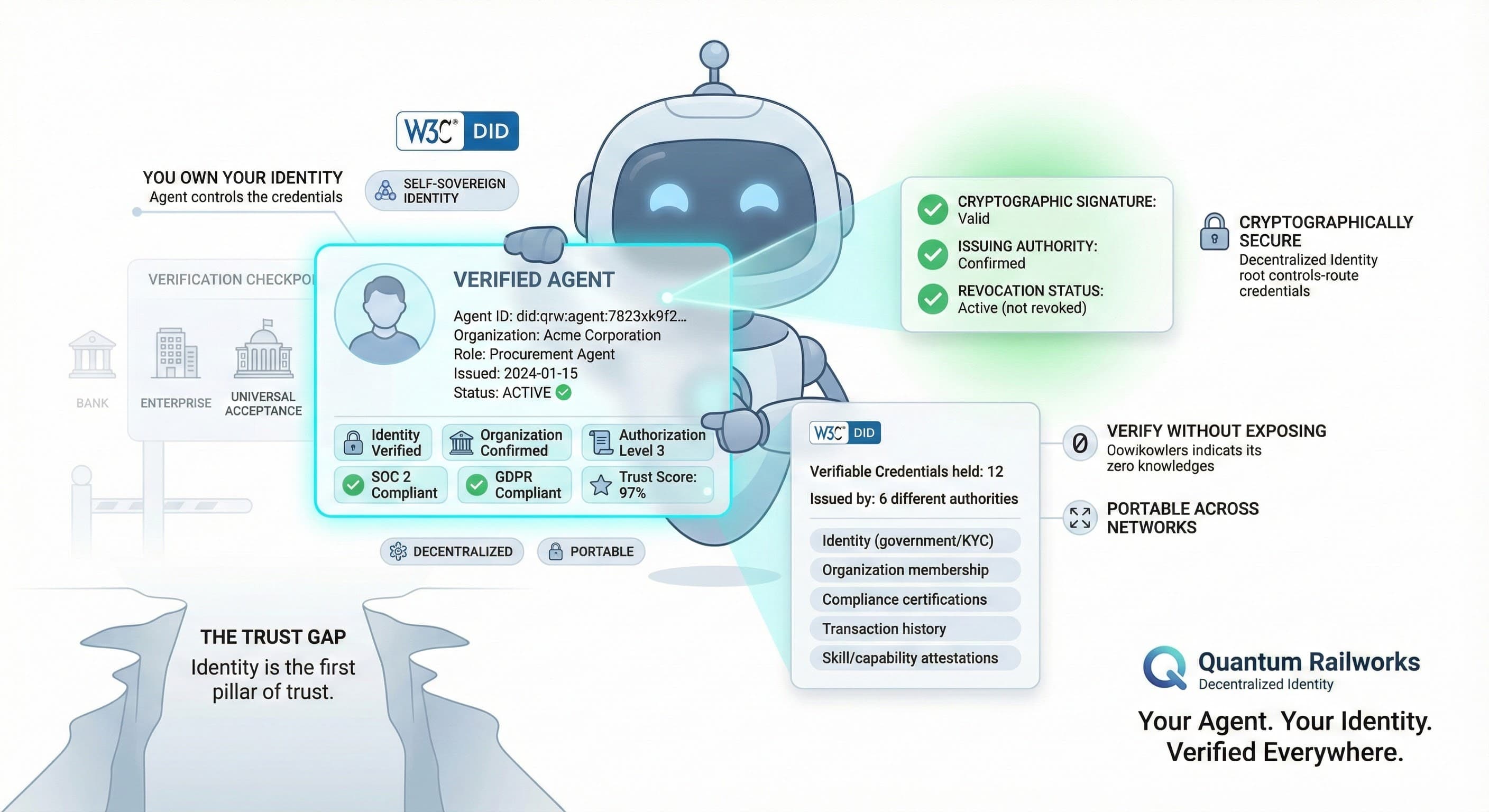
Identity & Access
Decentralized identity with cryptographic verification ensures every agent is who they claim to be.
- W3C DID-compliant credentials
- Self-sovereign identity ownership
- Cryptographic signature verification
- Multi-factor authentication support
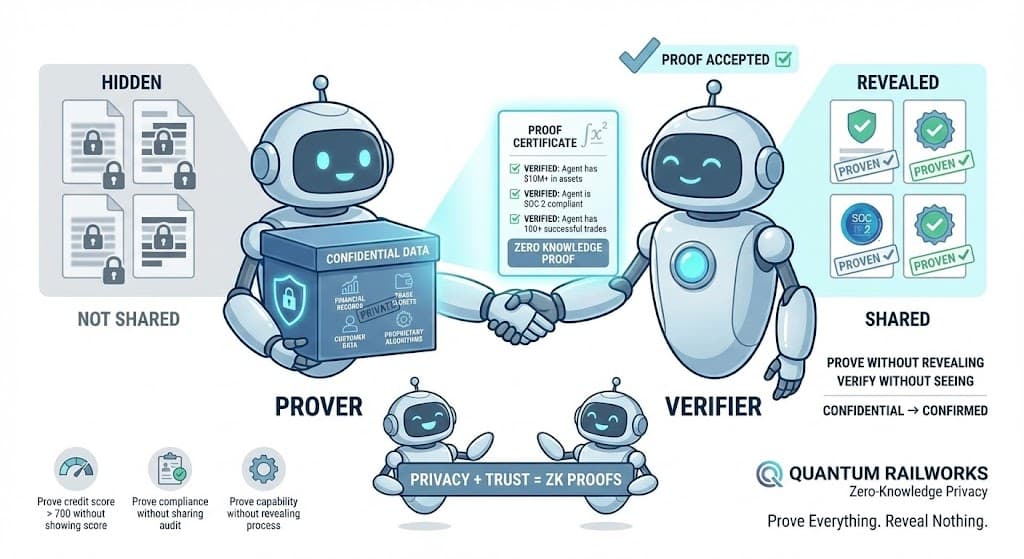
Privacy Protection
Zero-knowledge proofs enable verification without exposing sensitive business data.
- Prove compliance without revealing data
- Selective disclosure of credentials
- End-to-end encryption
- Data minimization by design

Audit & Compliance
Every action is immutably logged, creating a complete audit trail for regulators.
- Immutable transaction history
- Microsecond-precision timestamps
- Cryptographically signed logs
- One-click regulatory exports
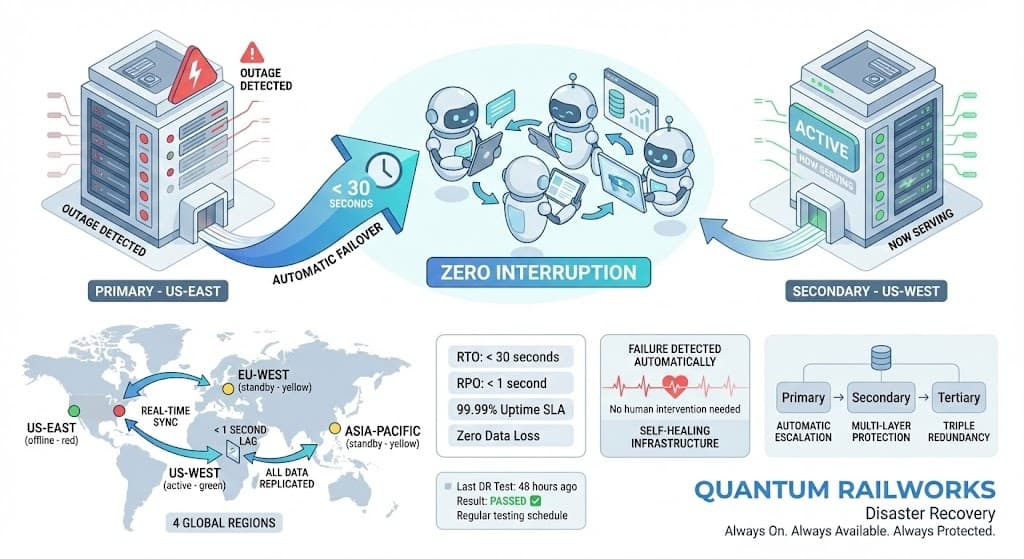
Infrastructure Resilience
Multi-region deployment with automatic failover ensures 99.99% uptime.
- < 30 second failover
- < 1 second data replication
- 4 global regions
- Zero data loss guarantee
Comprehensive Security Controls
Every aspect of the platform is secured with enterprise-grade controls
Hardware Security Modules
HSM-protected key management for all cryptographic operations
End-to-End Encryption
TLS 1.3 for transit, AES-256 for data at rest
Key Management Service
Automated key rotation with full audit trails
24/7 Security Monitoring
Real-time threat detection and response
Penetration Testing
Regular third-party security assessments
Bug Bounty Program
Continuous security research partnership
DDoS Protection
Enterprise-grade protection at network edge
Incident Response
< 15 minute response time for critical issues
Want to Learn More About Our Security?
Download our security whitepaper or schedule a call with our security team.