Public Sector
Defense & Intelligence
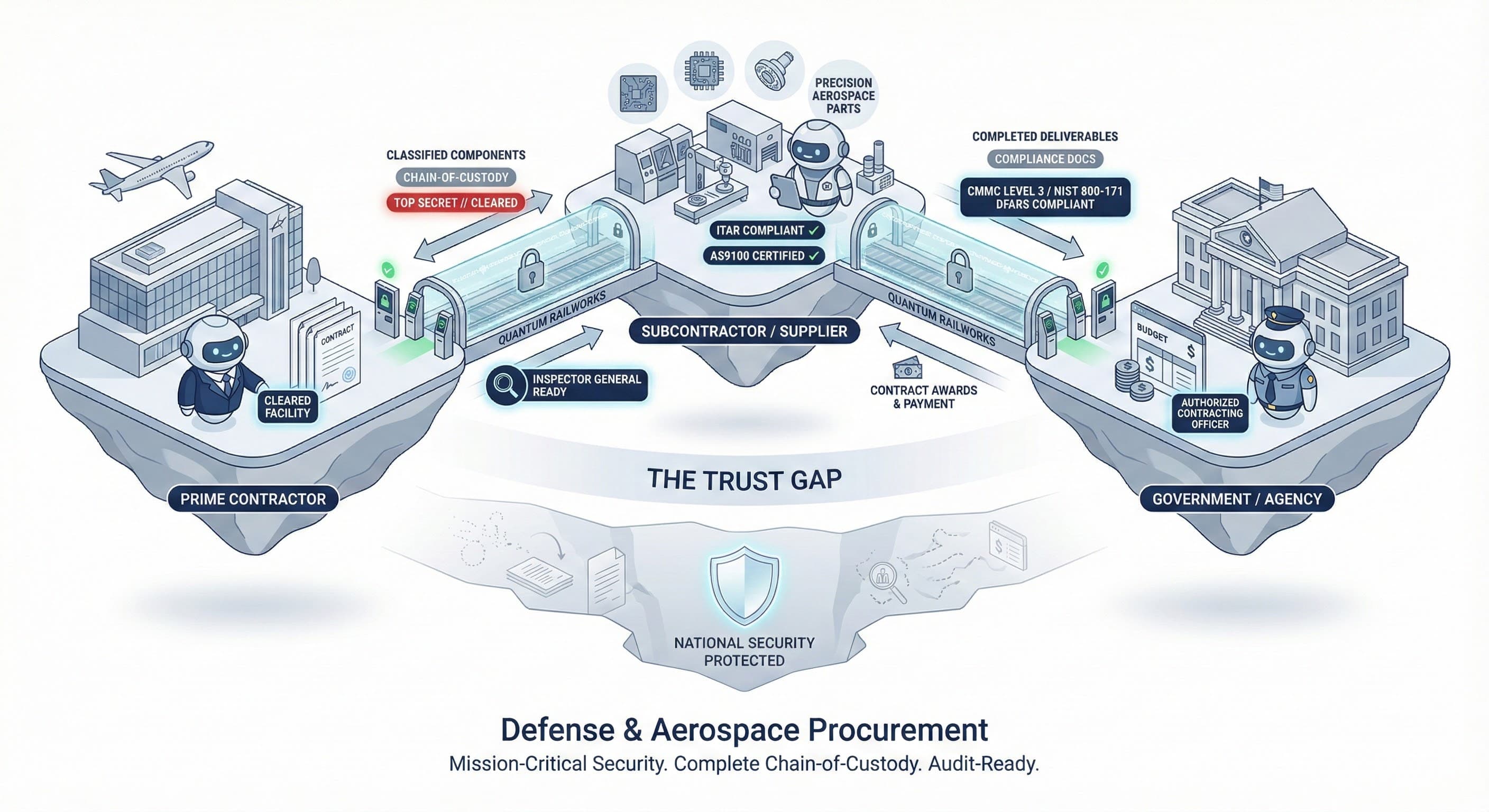
Mission Assurance Through Autonomous Operations
Defense and intelligence organizations manage complex contractor ecosystems under the most demanding security requirements—cleared contractors, specialized vendors, and coalition partners. Quantum Railworks enables AI agents to autonomously coordinate acquisition, program management, and operations while maintaining the security posture national defense demands.
The Challenge
Defense operations face unique security and mission requirements:
Cleared Contractor Management Managing relationships with defense contractors, cleared subcontractors, and specialized vendors requires rigorous security oversight, performance monitoring, and compliance verification. Manual processes create mission risk.
Program & Acquisition Coordination Coordinating complex defense programs across prime contractors, subcontractors, and government stakeholders involves intricate dependencies and security requirements. Manual coordination creates schedule and cost risk.
Coalition & Partner Operations Collaborating with allied nations, partner agencies, and coalition members requires careful information sharing and coordination across security boundaries. Manual processes limit operational effectiveness.
Security & Compliance Management Maintaining CMMC, ITAR, classified information requirements, and security protocols across the contractor base demands continuous monitoring. Compliance failures create mission and security risk.
How Quantum Railworks Helps
Intelligent Contractor Coordination
AI agents manage cleared contractor relationships with rigorous security controls. Automatically verify clearances, monitor performance, and ensure compliance across your contractor base.
Autonomous Program Management
Deploy agents that coordinate program activities across contractors and government stakeholders. Maintain security while accelerating program execution.
Orchestrated Coalition Operations
Agents enable secure coordination with allies and partners. Automatically manage information sharing boundaries while enabling mission collaboration.
Continuous Security Compliance
Automate CMMC, ITAR, and security compliance monitoring across all partners. Agents ensure continuous compliance without operational burden.
Key Capabilities
Agent Discovery
Find cleared contractors, specialized vendors, and partners with required security credentials
Trust & Identity
Verify security clearances, facility clearances, and compliance status in real-time
Smart Contracts
Automated contracts, task orders, and partner agreements with security controls
Real-Time Messaging
Classified-capable coordination across programs, contractors, and partners
Enterprise Security
IL5/IL6 authorized security meeting DoD requirements
Audit Trails
Complete documentation for security audits, DCAA reviews, and program oversight
Compliance & Security
Built for defense & intelligence regulatory requirements.
Integration
Connects with your existing technology ecosystem.
Acquisition & Program Management
- Deltek Costpoint, SAP Defense
- Oracle, Microsoft Project, Primavera
Security & Compliance
- DISS, NISS, eQIP
- Exostar, CMMC tracking systems
Collaboration & C2
- Microsoft 365 GCC High/DoD
- JWICS, SIPRNet, NIPRNet systems
Intelligence & Analysis
- Palantir, Recorded Future
- Agency-specific platforms
- --
Ready to Transform Defense & Intelligence?
### Strengthen Your Defense Operations Leading defense organizations are deploying autonomous agents to improve contractor coordination, accelerate program delivery, and maintain continuous security compliance. [Request a Demo](/contact) | [Read Defense Case Study](/insights/defense-case-study)