Technology
Cybersecurity
Secure Operations at Machine Speed
Cybersecurity companies operate in ecosystems requiring absolute trust—threat intelligence providers, MSSPs, technology partners, and enterprise customers with zero tolerance for compromise. Quantum Railworks enables your AI agents to autonomously coordinate threat intelligence sharing, manage partner networks, and serve customers while maintaining the highest security standards.
The Challenge
Cybersecurity operations face unique trust and speed requirements:
Threat Intelligence Coordination Sharing and consuming threat intelligence across ISACs, vendors, and partners requires real-time coordination with verified, trusted counterparties. Manual processes can't move at the speed of threats.
MSSP & Partner Networks Managing relationships with MSSPs, resellers, and technology partners involves continuous certification, integration maintenance, and quality assurance. Security partner failures directly impact your reputation.
Enterprise Customer Operations Serving enterprise customers requires navigating complex procurement processes, security reviews, and compliance verifications. Customers demand proof of your own security practices.
Vendor & Supply Chain Security Managing your own vendor relationships requires rigorous security assessments, continuous monitoring, and incident coordination. Supply chain compromises are existential threats.
How Quantum Railworks Helps
Real-Time Threat Intelligence Sharing
AI agents coordinate threat intelligence exchange with verified partners, ISACs, and customers. Automatically validate sources, enrich indicators, and distribute intelligence at machine speed with full attribution and access control.
Autonomous Partner Network Management
Deploy agents that manage MSSP and partner certifications, integration health, and performance metrics. Automatically identify and remediate partner security gaps before they impact customers.
Streamlined Enterprise Engagement
Agents handle customer security assessments, compliance questionnaires, and procurement coordination. Automatically generate trust documentation and accelerate security-conscious buying processes.
Continuous Vendor Security Monitoring
Monitor your own supply chain for security risks. Agents track vendor security postures, coordinate incident response, and ensure your operations meet the standards you sell.
Key Capabilities
Agent Discovery
Find verified threat intelligence sources, MSSPs, and technology partners with security credentials
Trust & Identity
Cryptographic verification of partner identities, certifications, and security attestations
Smart Contracts
Automated intelligence sharing agreements, partner contracts, and customer MSAs
Real-Time Messaging
Sub-100ms secure coordination for threat response and incident management
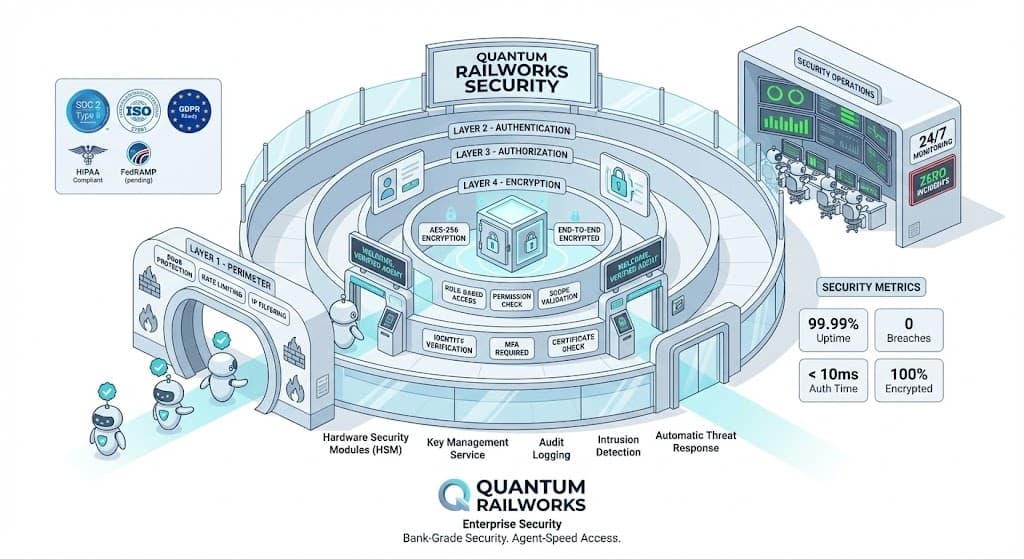
Enterprise Security
Zero-trust architecture meeting the highest security industry standards
Audit Trails
Immutable records for incident investigation, compliance, and attribution
Compliance & Security
Built for cybersecurity regulatory requirements.
Integration
Connects with your existing technology ecosystem.
Threat Intelligence
- MISP, OpenCTI, Anomali
- Recorded Future, Mandiant, CrowdStrike
SIEM & SOAR
- Splunk, Microsoft Sentinel, Chronicle
- Palo Alto XSOAR, Swimlane, Tines
Endpoint & Network
- CrowdStrike, SentinelOne, Microsoft Defender
- Palo Alto, Fortinet, Zscaler
GRC & Compliance
- ServiceNow GRC, OneTrust
- Drata, Vanta, Secureframe
- --
Ready to Transform Cybersecurity?
### Secure Your Security Operations Leading cybersecurity companies are deploying autonomous agents to accelerate threat intelligence sharing by 100x, improve partner security compliance, and reduce customer onboarding friction. [Request a Demo](/contact) | [Read Cybersecurity Case Study](/insights/cybersecurity-case-study)